Privacy Awareness Week Part IV – Privacy Priorities
By Cameron Abbott, Rob Pulham and Stephanie Mayhew
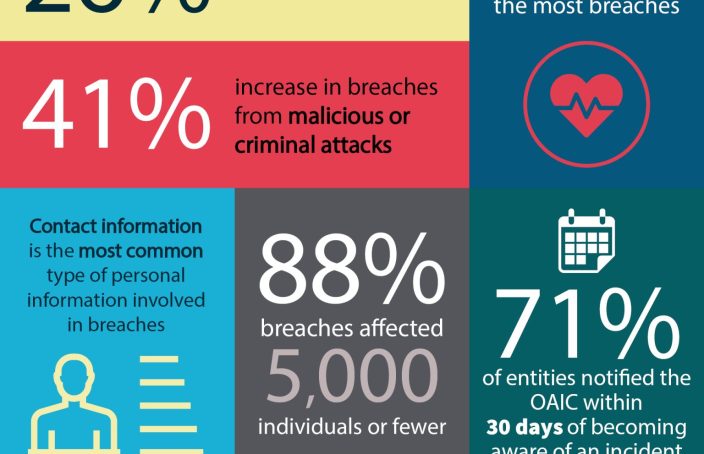
Given the current privacy reform and cyber threat environment, the question we get asked a lot is – what are the privacy risks that should be assessed in our organisation and how do we prioritise these? Unfortunately this isn’t always a ‘one size fits all’ answer but there are some basic matters you can check as to whether your organisation is considering privacy risks proactively.
Read More