By Cameron Abbott, Rob Pulham and Stephanie Mayhew
Over the past two years, the Privacy Act has been the subject of long-awaited reform in Australia however, it seems the Optus data breach may have given it some much needed momentum.
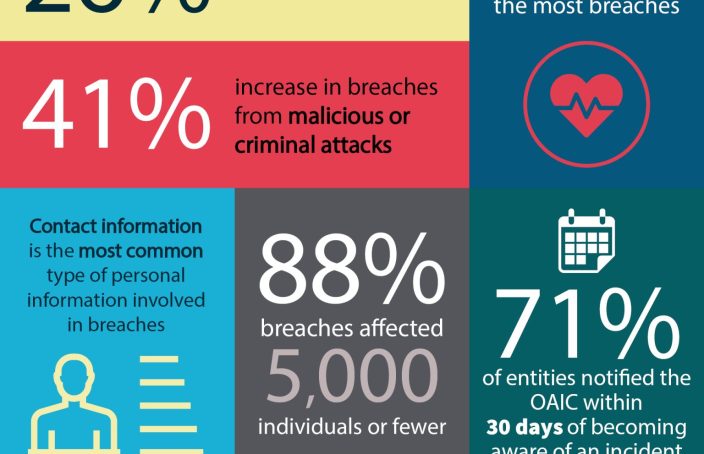
The Optus attack is understood to have affected the details of 11.2m Optus customers, and of that 2.8m individuals have had their driver’s licence and/or passport numbers compromised. The hacker claims to have extracted the data from an API – software that allows two different systems to talk to each other. Therefore, if the claim is true the hacker didn’t need to provide authentication (e.g. a username and password) to retrieve the data.
In the wake of the attack, the Government has shared its plans to pursue substantial reforms that will include increased penalties under the Privacy Act (currently capped at $2.22m per offence) as well as changes to data breach notification laws to allow companies to rapidly inform financial institutions of affected individuals in an effort to minimise fraud.
The data breach also highlights the risks involved in collecting large amounts of personal information and storing this for excessive time periods. While the Privacy Act promotes the collection of a minimum amount of personal information, i.e. only that information that is necessary for a particular purpose and which the entity intends to use or disclose – individuals generally have limited control over how long their information is retained for.
During the initial stages of the Privacy Act review, the Attorney General’s Department sought submissions from entities on their views as to whether individuals should be given the right to have their personal information erased. Optus in submissions to the review argued against such a change stating that the right to erase personal data would involve significant technical hurdles and compliance costs that would outweigh the benefits. Of course this incident has happened just as stores are gearing up for Halloween – a fitting time for those public submissions to come back to haunt them.